How to Pass Strong Integrity Using Revoked/Banned Keybox File
Yes, you read that write! Using a nifty workaround [or a loophole from Google’s end], you can now pass the Strong Integrity test even using a revoked/banned keybox XML file. One of the biggest issues with these keybox files is that they tend to get revoked within a week. Then I had to be on my toes, searching for a new unrevoked file, and sharing it with you.
While that’s fine, what isn’t is the fact that many people have started selling these files, and the users who are in utter desperation to pass the Strong test are left with no choice but to buy those files. Well, not anymore! Both my misery [searching for files] as well as the users [who were purchasing these files] are now finally coming to an end.
However, it goes without saying that this honeymoon period isn’t going to last long. Once Google finds out about it, it will patch it at the earliest. But until that happens, let’s extract maximum benefits out of it. Follow along.
- How to Pass Strong Integrity Using Revoked/Banned Keybox XML File METHOD 1: Via Spoofing METHOD 2: Without Spoofing [NEW] METHOD 3: Lengthy One
- An Important Note About Keybox
How to Pass Strong Integrity Using Revoked/Banned Keybox XML File
Before starting, please take a complete device backup. Droidwin and its members wouldn’t be held responsible in case of a thermonuclear war, your alarm doesn’t wake you up, or if anything happens to your device, and data by performing the below steps. [Credits: XDA Senior Member zgfg].
METHOD 1: Via Spoofing
- First off, uninstall Play Integrity Fix/Fork module that you have installed.
- Then, flash the Play Integrity Fix Inject Manual module onto your device.
- Now restart your device. Then install KSUWebUI and give it the SU access.
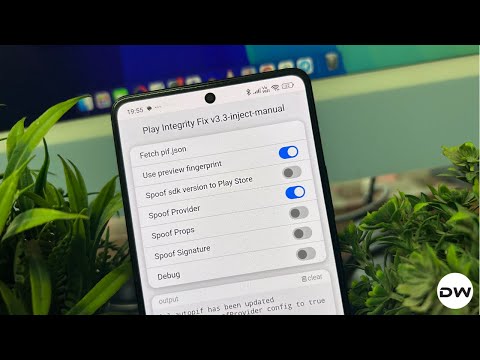
- Now launch it and select Play Integrity Fix [Inject]. Then tap on Advanced.
- Finally, enable the toggle next to Spoof Provider and check out the results.
METHOD 2: Without Spoofing [NEW]
While spoofing does allow you to pass Strong Integrity on a banned or revoked keybox, it also has some adverse impacts on several Google apps, such as Google Pay [for some users, even the Play Store is not working after carrying out this tweak]. So in this guide, I’ll show you how to pass Strong even without carrying out any spoofing. Follow along.
- Make sure you have checkmarked all the other prerequisites beforehand.
- Then launch KSUWebUI > Tricky Store > tap on the hamburger menu.
- Select Add System App and hit the minus icon next to these two apps: com.google.android.gms com.google.android.gsf
- That’s it. Now perform a check, and you’ll pass the Strong Integrity test.
METHOD 3: Lengthy One


- First off, get a banned/revoked keybox file from here . [See NOTE below].
- Then, uninstall the Tricky Store and Play Integrity Fix/Fork module.
- Now, launch a root-supported file manager app like Solid File Manager.
- Then head over to data/adb and delete the folder of tricky_store.
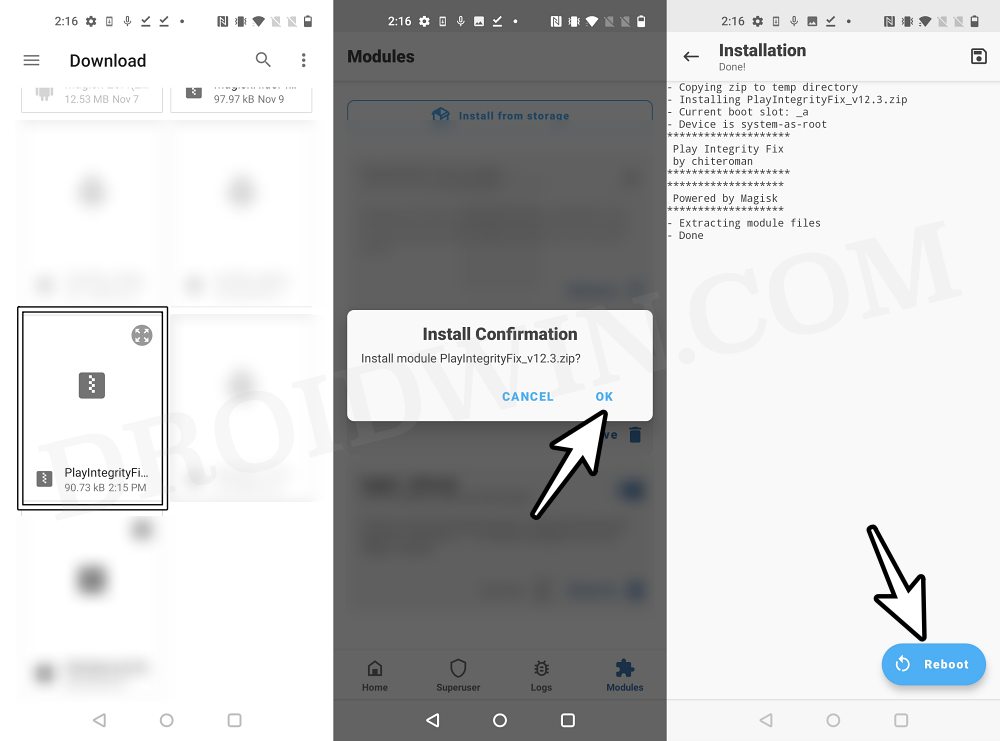
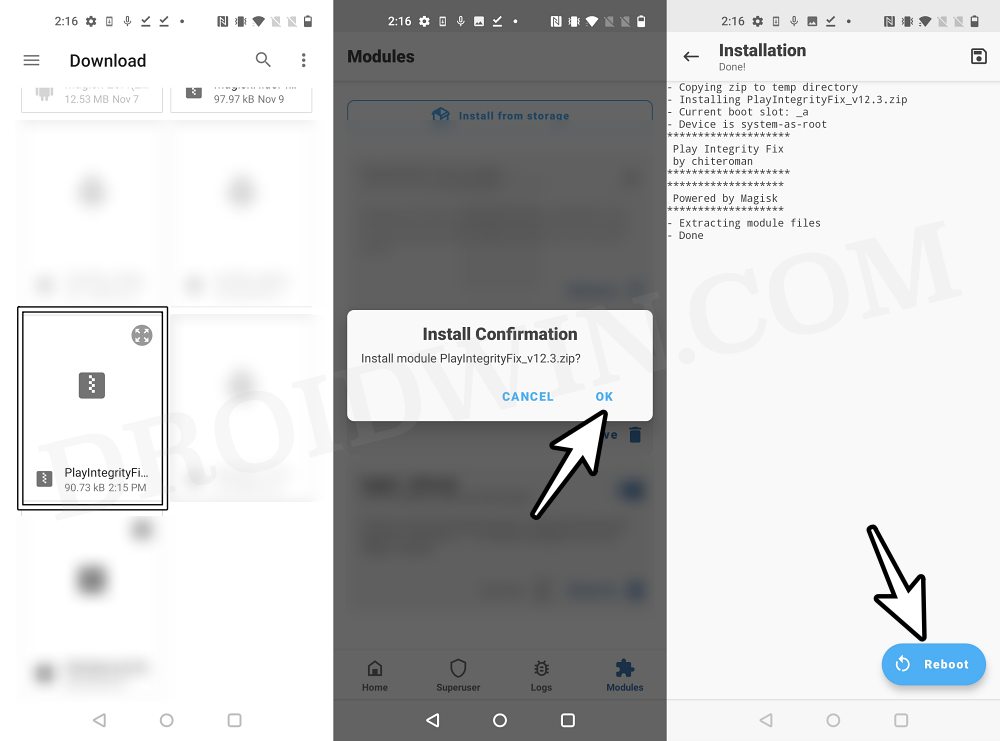
- Now, launch Magisk and flash the Tricky Store and Play Integrity Fork CI modules.
- As opposed to Play Integrity Fix, the Play Integrity Fork doesn’t automatically give us a fingerprint file [pif.json], so let’s manually invoke it from the module.
- For that, download and install wget2 [Credits: XDA Senior Recognized Developer / Contributor: osm0sis]
- Then install Termux , launch it, and execute the following commands: su //you’ll get a SU request, hit Grant cd /data/adb/modules/playintegrityfix //to change the directory to the module’s sh autopif2.sh –preview // this will give you the fingerprint file
- Now launch Solid File Manager and head to the below location: data/adb/modules/PlayIntegrityFix
- Open the custom.pif.json file, add the following values at the end, and save it. // Advanced Properties “spoofBuild”: “1”, “spoofProps”: “1”, “spoofProvider”: “1”, “spoofSignature”: “0”, “spoofVendingSdk”: “0”, “verboseLogs”: “0”
- Then go to the below location and create a blank security_patch.txt file: data/adb/tricky_store
- In the same location, open the target.txt file.
- Then add the first two values and comment the third one via hash, as shown [you may leave the other values as it is] android com.android.vending #com.google.android.gms
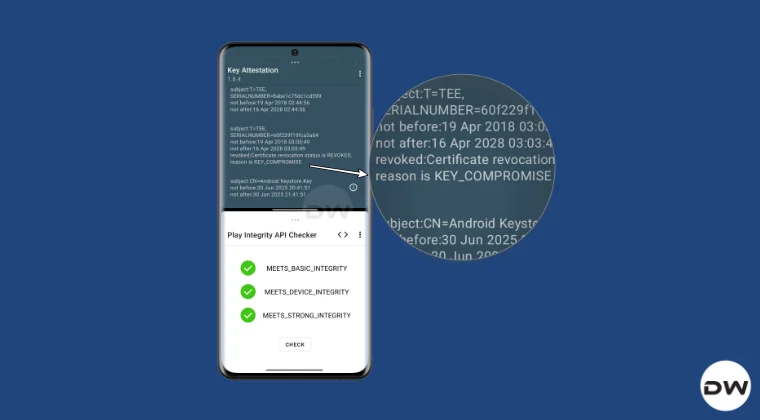
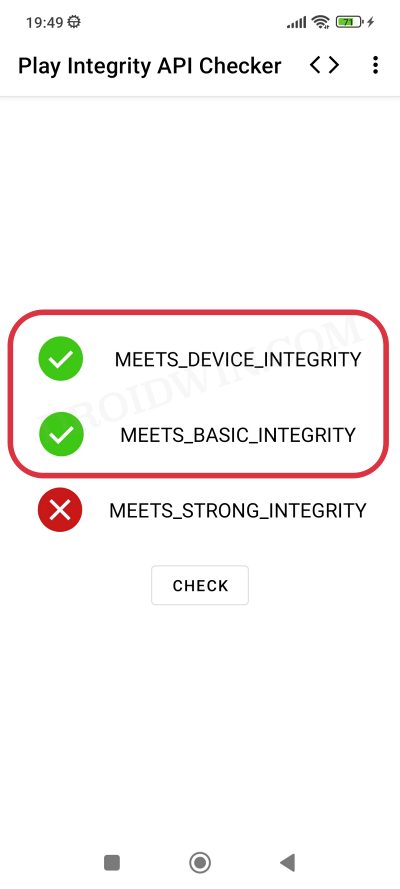
- Finally, hit Save. Now launch Play Integrity API Checker and check out the result. Three greens are all yours!
An Important Note About Keybox
While the keybox can be banned or revoked, it should not be expired. To verify it, install Key Attestation from GitHub and check out the “not-after” date in the third paragraph [in our case, it is 16th April 2028]. Theoretically, if Google doesn’t find out this loophole, then we can use these keybox till 5-6 more years [I have a bunch of revoked keybox whose expiry date is 2030].
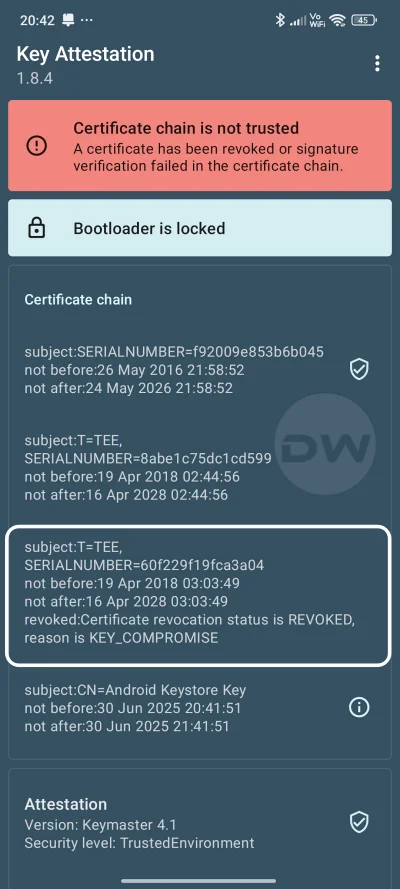
Moreover, you can also see in the very same paragraph, you can see that: revoked: Certificate revocation status is REVOKED, reason is KEY_COMPROMISE. This all but proves that we are using a revoked keybox XML file, and using that, we are passing the Strong Integrity test.
- How to Pass Play Integrity in New Android 13+ Checks
- Play Integrity Error Getting Token from Google: How to Fix
- How to Pass Play Integrity on LineageOS ROM [any version]
- Use Custom Fingerprint/Build.Prop to Pass Play Integrity Test
- jjyang 2 months ago Reply plz Give me the latest available key. plz~
- chris 4 months ago Reply Hi, I’ve tried the 3rd method you’ve supplied, and I still failed the strong and device :(. Can you send me an email, maybe we could try to work this out?
- Junaid 6 months ago Reply Sir can you please share keybox XML file. Play integrity file please
- Lucho 6 months ago Reply Please send me the xml file.
- Ujjwal R 7 months ago Reply Can you show to use banned/revoked keybox in custom rom without root and edit files with custom recovery
- Urias Uhle 7 months ago Reply Hello i need a keybox.xml file my phne ist Poco X3 NFC with DerpFest Running
- david 7 months ago Reply keybox please
- Imtiaz 7 months ago Reply Send me the Keybox file?
- Mukesh 7 months ago Reply My phone is oneplus Nord 4. Plz send xml file
- WhatTheFuckDude 7 months ago Reply Quit deleting my questions punkass
- Ritik 7 months ago Reply Please send me the file to kalungai22@gmail.com I have to pass all 3 integrity test
- Raul 7 months ago Reply I have Magisk. Is it better to switch to APatch? Is APatch better than Magisk for hiding root?
- Imtiaz 7 months ago Reply Send me keybox file bro
- Sandip 7 months ago Reply Can you please send me the file
- Yovie 7 months ago Reply Hallo kak .. boleh minta keybox.xml nya 🙏sebelumnya TerimaKasih
- Billou 7 months ago Reply Hello, I used your guide to install KernelSU and SUSFS. I followed all the instructions to pass the integrity test, but unfortunately, the tests are still failing regardless of which modules I use. I’d appreciate it if you could either provide a banned/revoked keybox file for testing purposes or guide me through the process again to identify what might be going wrong. Thank you in advance for your help! Best regard
- jimmy 7 months ago Reply Hey bro, can I have a revoked keybox? Thank you.
- Elo 7 months ago Reply Gives me only device integrity
- Elo 7 months ago Reply Where to paste revoked keybox?
- Antonis 7 months ago Reply cant make revolut work…. any idea?
- thomas 7 months ago Reply I did exactly you instructed but Wallet still does not work. Sadique Hassan 7 months ago Reply Hey mate, can you try out the steps mentioned here [just replace WhatsApp by Wallet]: https://droidwin.com/how-to-run-whatsapp-on-rooted-unlocked-bootloader-devices/ DigiBombardo 7 months ago Reply Key attestation shows my keybox is not compromised, but no matter what i do above or with the whatsapp link, it will not show my bootloader locked. Bootloader spoofer shows 404 error on the link above. DigiBombardo 7 months ago Reply The only issue with my phone certification is that it sees the bootloader as unlocked. My keybox does not show compromised in the key attestation app, but it still shows bootloader unlocked. In the WhatsApp link, the bootloader spoof shows 404 error when going to the site.
(Cancel Reply)
Δ
Use Custom Fingerprint/Build.Prop to Pass Play Integrity Test
In this guide, we will show you two different methods to create custom fingerprints/build.prop to pass the Play Integrity Test on your rooted device or if you are running a custom ROM. Well, it seems we might finally reach the end of the road, as far as gaining administrative privileges is concerned. For the unaware, if you root your device, then it will trip the SafetyNet Test, thereby making it difficult to use banking and payment apps.
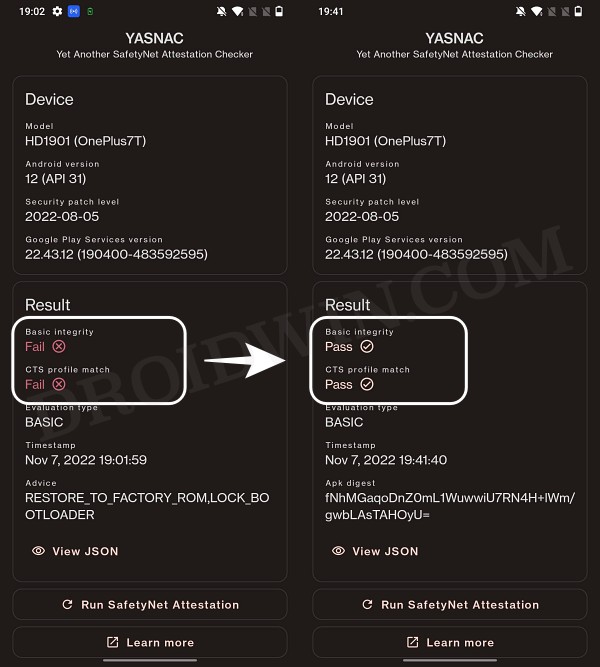
However, we managed to find a workaround that helped us pass this test with ease . Fast forward to this year, Google introduced the Play Integrity Test and has instructed every app to incorporate its API by January 2025. At the time of writing, many banking and payment apps have already shifted over to this test.
As before, if your device is rooted, then you will fail this test, thereby resulting in your inability to use banking apps. Fortunately, we once again managed to get hold of a method to bypass this test . Google then took a step further and patched our tweak only for us to bypass it once more! Until now. The Silicon Valley giant has finally taken the most extreme step to date which might finally spell the end of root for the tech enthusiasts.
- Google ‘Banning’ Fingerprints for Play Integrity: Is Hiding Root Impossible?
- How to Create and Use a Custom Fingerprint/Build.Prop to Pass Play Integrity One Click Method [Easiest] Create a New Fingerprint JSON File Manually Some Additional Tips on Creating Custom JSON Files Pixel Flasher Tool [Recommended]
- What if the Test Fails? Repeat and Repeat!
- Rooting and Custom ROMs: A Difficult Yet Achievable Journey Ahead!
- UPDATE: List of Fingerprints Build Prop Passing Play Integrity
Google ‘Banning’ Fingerprints for Play Integrity: Is Hiding Root Impossible?
Up until now, we were able to use the XDA Senior Member Chiteroman’s module to easily pass the MEETS_DEVICE_INTEGRITY and MEETS_BASIC_INTEGRITY, which are two prerequisites of the Play Integrity test. In hindsight, the module uses a fingerprint from one of the unpatched devices and the developer then uploads his mod over to GitHub. Since this mod is open source, anyone can easily decode it, including Google! And that is exactly what is happening.
While it might sound hard to digest why would Google end up utilizing a part of its resources towards this project which affects only about 3% of Android users, but trust us, that’s exactly what’s currently going on. The developer has tried out numerous combinations of fingerprints in its modules, including different OEMs, different Android versions, and even different custom ROMs [such as Evolution X].


However, every time a new module is released, Google tends to patch it straightaway, thereby leaving the developer with three options- either keep on playing this trial-and-error method, make the module closed source, or list out the instructions on how a user could create a custom fingerprint file and use it to pass this test.
The first approach was neither the most feasible nor the most viable for him [because he wasn’t earning anything from it and more importantly he has a life out of this modding community too!]. Likewise, making it a closed source might have raised a few eyebrows from some of the users [though judging by his reputation, that shouldn’t happen in the first place]. Henceforth, the third option is our best bet.
How to Create and Use a Custom Fingerprint/Build.Prop to Pass Play Integrity


There exist a couple of methods of getting this job done- the automatic and the manual way. In the automatic method, you would still need to carry out the first step from the manual method, but it will then take care of the rest of the steps. Moreover, please take a backup beforehand, just to be on the safer side. Droidwin and its members wouldn’t be held responsible in case of a thermonuclear war, your alarm doesn’t wake you up, or if anything happens to your device and data by performing the below steps.
One Click Method [Easiest]
Well, we can’t thank chiteroman enough for this! He has just released a plug-and-play version of this module which would be the easiest and best method to opt for the generic users. All you need to do is get hold of this module v14.2 from GitHub , enable Zygisk, flash it via Magisk, and delete the data of Google Services Framework, Play Store, Play Service, and Play Protect Service [if present]. Here’s a detailed guide on the same , it’s highly recommended you check it out.
Create a New Fingerprint JSON File Manually
XDA Senior Recognized Developer Osmosis took this responsibility on his shoulders and has done quite an excellent job in listing out the steps on how you could create and use a custom.pif.json. Here are the instructions steps for the same:
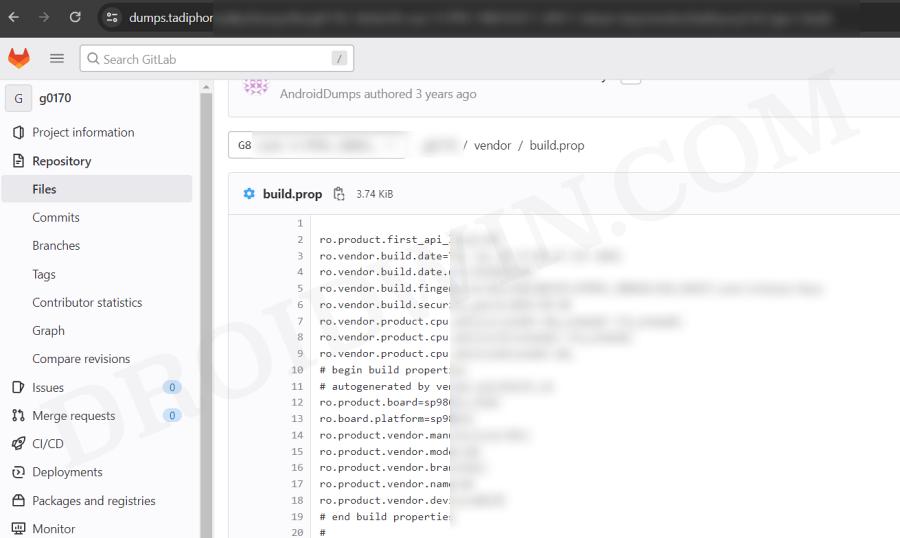
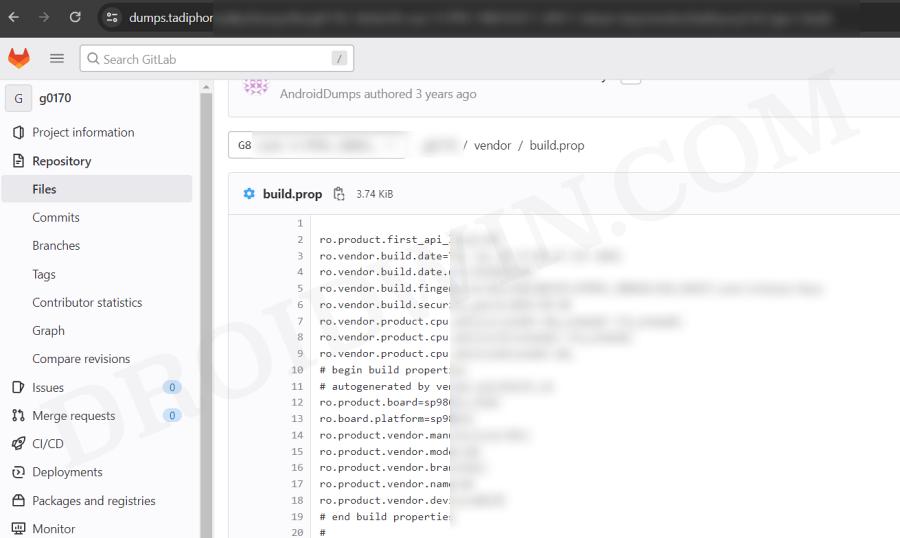
[Check out UPDATE section at the end of this guide!] First and foremost, download the stock ROM for a random device [see below], extract it, and get the system build.prop and/or product build.prop and vendor build.prop files from it. [In some cases, you could simply get hold of the firmware DUMP file directly on websites like Gitlab. So it’s better if you can find the dump because then you wouldn’t have the download the ROM and neither would you have to extract these files].
We cannot share these files/details publicly because Google will get hold of them and mass ban all of them at once [it has just happened with an Asus device. We managed to get an unpatched fingerprint from one of the Asus devices and used it to pass the Play Integrity Test. This worked for a few days before being ultimately patched by Google!]. Regarding “a random device” that we mentioned above, make sure to keep the following points in mind before you download its ROM:
- All older Nexus devices (Nexus 6/shamu and older) appear to be banned.
- Final release ROM builds of all no-longer-supported remaining Nexus and Pixel devices are banned.
- The device must have at least been upgraded to Oreo (Android 8) and should have come with at least an Android 6 or higher version out of the box.
- Devices launching with Pie (Android 9) or later might not work.
- In a nutshell, try to pick a combination of a device and its ROM which you don’t think many people will choose. This is because “The less obvious statistical data Google receives indicating a particular fingerprint is being abused, the fewer fingerprints will get banned”.
- Don’t go for the likes of Pixel, Samsung, Xiaomi, and other popular OEMs as most of their fingerprints have already been used or patched by Google. Instead, go for less-known brands such as Asus, Vivo, Oppo, or other Chinese brands that not many know about. Remember, the less popular a device is, the better your chance of passing the Play Integrity test!
Let’s now talk about the location of build.prop, product, and vendor.prop. In case of build.prop, it could be found at /system/system/build.prop or /system/build.prop. The product can be /product/build.prop and/or /product/etc/build.prop. The vendor is located in /vendor/build.prop or/system/vendor/build.prop.
In general, they’ll be ro.build.fingerprint + ro.product.* (older system build.prop), or, ro.system.build.fingerprint + ro.product.system.* (newer system build.prop) [or, ro.product.build.fingerprint + ro.product.product.* (product build.prop, only needed on devices where system build.prop contains “generic” values)].
From there, you’ll have to copy the following six values: PRODUCT (ro..name), DEVICE (ro..device), MANUFACTURER (ro..manufacturer), BRAND (ro..brand), MODEL (ro..model), and FINGERPRINT (ro..fingerprint). Optionally, also copy SECURITY_PATCH (ro.build.version.security_patch from system build.prop)
Any build prior to March 16, 2018 does not require a matching SECURITY_PATCH field, though adding it wouldn’t be of any harm. Moreover, do note that the date should be from the ro.build.date present in the system build.prop, instead of the AOSP base date in the fingerprint.
Now paste the copied values between the quotes of the corresponding fields in the template custom.pif.json sample shown below [it’s just a sample one that has already been banned by Google. So make sure to replace the values accordingly].
{
"PRODUCT": "taimen",
"DEVICE": "taimen",
"MANUFACTURER": "Google",
"BRAND": "google",
"MODEL": "Pixel 2 XL",
"FINGERPRINT": "google/taimen/taimen:8.1.0/OPM4.171019.021.R1/4833808:user/release-keys",
"SECURITY_PATCH": "2018-07-05",
"FIRST_API_LEVEL": "26"
}
Here’s another JSON file with slightly more information:
{
"MANUFACTURER": "Google",
"MODEL": "Pixel 2 XL",
"FINGERPRINT": "google/taimen/taimen:8.1.0/OPM4.171019.021.R1/4833808:user/release-keys",
"BRAND": "google",
"PRODUCT": "taimen",
"DEVICE": "taimen",
"RELEASE": "8.1.0",
"ID": "OPM4.171019.021.R1",
"INCREMENTAL": "4833808",
"TYPE": "user",
"TAGS": "release-keys",
"SECURITY_PATCH": "2018-07-05",
"DEVICE_INITIAL_SDK_INT": "26"
}
Once you have got the required information, save it in a text file and rename it to custom.pif.json if you are using the fork of the original module [by Osmosis, which we are using] or pif.json [if you are using the original module by Chiteroman]. After that, you’ll now have to transfer the file to your device.
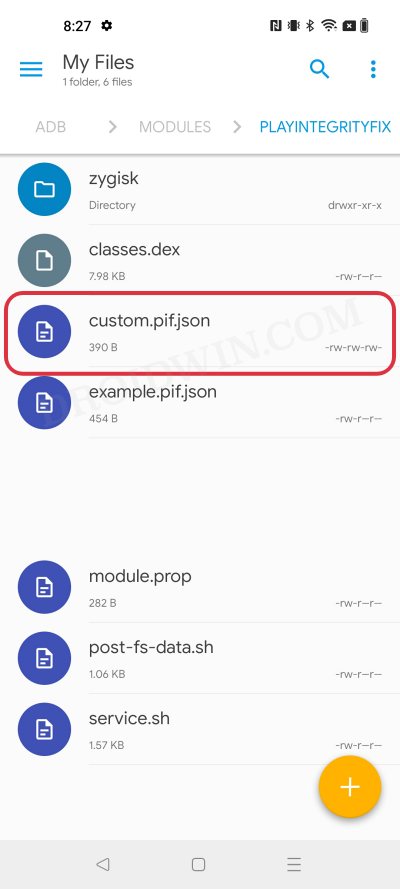
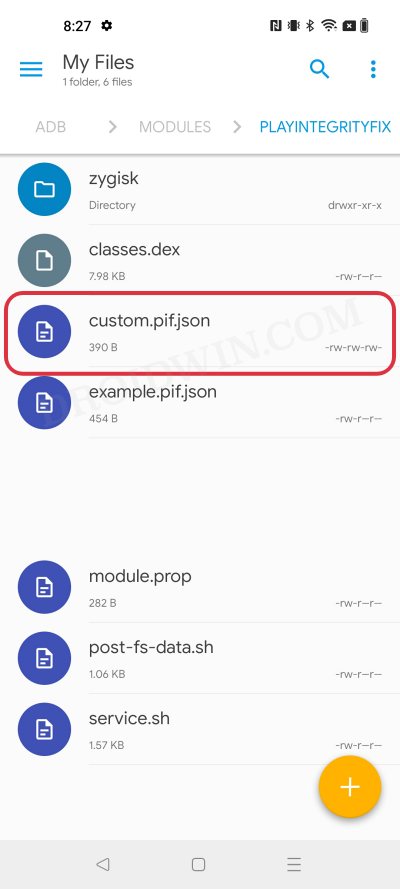
For that, you could either do so via the Pixel Flasher Tool as explained in the next section, or by copying your .json file to /data/adb/modules/playintegrityfix/custom.pif.json [for Osmosis, in our case] or /data/adb/pif.json [for Chiteroman]. Once done, restart your device and then check if it passes the Play Integrity Test using this custom fingerprint/build.prop! If it doesn’t, then you’ll have to pick a different fingerprint and retry this process.
Some Additional Tips on Creating Custom JSON Files
- Let’s say that a device was released with Android 8, and then it received subsequent updates to Android 9 and 10. This way you’ll be able to create three different fingerprint JSON files to test. However, most of the details will be the same in all those files, such as MODEL, BRAND, MANUFACTURER, and even the FIRST API LEVEL because the device was initially launched with Android 8, that fact isn’t going to change irrespective of the current OS.
- Moreover, there needs to be a comma after the end of every line in the JSON file, except the last line [as is evident from our above example.
- If you still have any doubts with regard to your JSON file, then you could use this JSON Validator and it will point out all the errors in your file, if any.
Pixel Flasher Tool [Recommended]
The tool supports two methods- it could either generate a random fingerprint JSON file for you or you could create and upload your own custom fingerprint. If you ask the tool to generate a JSON file for you, then it has a high chance of getting patched by Google as opposed to the one that you have created manually. However, as opposed to the manual creation, it will take a lot [and yes, we really mean a lot] of time and effort. So decide on this trade-off accordingly.
- To begin with, get hold of the build.prop file from the desired firmware version as explained above.
- Then download and extract Android SDK Platform Tools on your PC.
- After that, enable Zygisk via the Magisk’s settings menu and restart your device.
- Now download Pixel Flasher from GitHub and launch it [credits: XDA Recognized Developer badabing2003].
- Then click on Browse > navigate to the platform-tools folder and select it.
- Now click on Scan and select your device from the list.
- Then click Magisk > Install PIF module and select the desired one [we have chosen Osmosis].
- The latest version of the mod will now be installed. Once done, hit OK and click Reboot System.
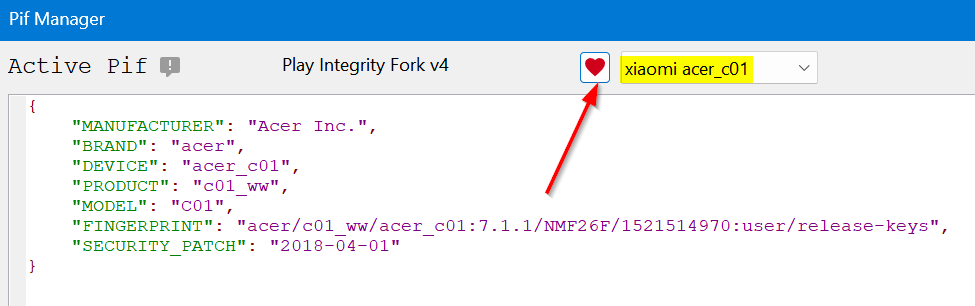
- Once your device boots up, click on PIF Manager [it will be empty as of now].
- Now, if you want to opt for the Manual Method , then click on Process build.prop(s) , navigate, and select your build.prop files. The order of precedence is as follows: build.prop system-build.prop system.prop product-build.prop product.prop vendor-build.prop vendor.prop Any other prop file
- The tool will now read these files and bring up the output something as shown in the below screenshot.
- On the other hand, for Automatic Method , click on the Get TheFreeman193 Random Pif button. It will populate the output window with the data from a random device.
- Once done, click on the Paste button next to Output and the data will be populated under the Active PIF section.
- At this stage, you should see the red warning next to Active PIF. This just indicates that the contents of the Active PIF window are not the same as the contents on the device.
- So click on Create PIF.json and the file will be transferred to your device. Likewise, the red warning should now turn gey, meaning the content of PIF widow is the same as that on your device.
- Finally, download and install a SafetyNet Checker app out of the four listed there. As of now, we are going ahead with Play Integrity API Checker.
- So click on Play Integrity check. It will launch the Play Integrity API Checker app, perform the test, and display the result in the output window.
- If it passes the device integrity and basic integrity tests, then congrats, you have found the needle in the haystack! But what if the test fails? Let’s find out.
What if the Test Fails? Repeat and Repeat!
- If you have chosen the Manual Method and failed the test, then you’ll have to get hold of a new JSON file from different firmware and repeat the above steps. Do so until you get the right JSON file that passes both these tests.
- If you have chosen the Automatic Method , then in that case, click on the Get TheFreeman193 Random Pif button > click on Paste next to Output. Then click on Update PIF.json > Play Integrity Check. It will perform the check and display the result. Keep on carrying out these processes until you achieve success.
Moreover, as soon as you find the right fingerprint JSON file, make sure to hit the heart icon and save that file. And please don’t share it with others as upon doing so, the chances of it getting into the hands of Google and subsequently nullifying it by the Silicon Valley giant increases tremendously. [So sharing is not caring in this case!].
Rooting and Custom ROMs: A Difficult Yet Achievable Journey Ahead!
So this was all from this guide on how to use a custom fingerprint/build.prop and pass the Play Integrity Test. While we always believed in the “sharing is caring” motto, however, for once, let’s not adopt it in this case scenario. If you get hold of a working fingerprint and then end up sharing that with the rest of the users, then it will ultimately be patched by Google. So keep that unique build.prop with yourself and prevent it from getting caught by Google!
NOTE: Some or the other changes are being constantly implemented by Google at an alarming rate. Thankfully, the developers are always one step ahead and are testing out new ways of bypassing the patches enforced by the Silicon Valley giant. But this also means that you will witness changes to the modules at frequent intervals as well, so we will update this guide as and when that happens. Make sure to keep a tab on this post regularly. [Screenshots Credits, unless specified otherwise: XDA Recognized Contributor badabing2003].
UPDATE: List of Fingerprints Build Prop Passing Play Integrity
Well, we decided to do all the dirty work on your behalf by compiling a list of all the custom fingerprints/JSON/build props from the devices that pass the Play Integrity tests. However, make sure you’re the earliest adopter of these builds, or else, it won’t be long before others get their hands on them. With that said, even if these get patched by Google, we will generate a new one at the earliest. So make sure to keep a tab on the below linked guide frequently.
List of custom fingerprints/JSON/build prop that pass Play Integrity
- sonn 2 months ago Reply Send me XML file to pass device integrity
- Shadman 4 months ago Reply Hellloo pleaseee send keybox.xml Email : shadmanahmadixo@gmail.com
- Ameer 11 months ago Reply Send me XML file to pass strong integrity Skye 9 months ago Reply Please give me keybox.xml Thank you
- Milan Čížek 2 years ago Reply Hi, I have extracted all three build.prop (system,product,vendor) from original stock image – extracted all *.img via payload-dumper-go.exe from payload.bin + ext2explore.exe. But I am not able to load the prop to PIF Manager, it always ends with the error. File “pif_manager.py”, line 1051, in process_props AttributeError: ‘PifManager’ object has no attribute ‘first_api’ https://pasteboard.co/UioQok8ehMt9.png What is wrong? ro.product.first_api_level=30 is in vendor-build.prop ro.board.first_api_level=30 too
- Tjw 2 years ago Reply Thanks for this guide. I can finally get a working custom file. I appreciate this simplified explanation and it’s straight forward enough for me to get this working. Well done author!! Thanks
- Jonathan 2 years ago Reply get the system build.prop and/or product build.prop and vendor build.prop files from it. How? Milan Čížek 2 years ago Reply You have to download stock image for your phone and then extract them from system/product/vendor.img files. Swastik Singh 8 months ago Reply Pls XML file or file links to solve the issue of safety internet pass problem . in poco f5 matrixx os
- kryspus 2 years ago Reply hello, I have downloaded 4 differents rom, could you explain how to extract the system to get in to it? Thx
- kryspus 2 years ago Reply Hello i have hiting facing the wall while i wanted to unpack stock rom to see the right files. It’s looks like a quite a challenge, can i expect any advice here? It’s unbelievable how much GB’s i have to download from internet and a bunch of tools to get a few lines of code.
- Jimmy 2 years ago Reply Thank you for this guide. I have just discovered today that many of my apps are refusing to work because of this problem. Cheers
(Cancel Reply)
Δ