How to Run Banking Apps on Rooted Android Device [14 Methods]
In this guide, we will show you ten different methods using which you can run banking apps on your rooted Android device. Rooting is no longer what it used to be. Not only has the entire process undergone a major change thanks to the introduction of the init_boot partition, but the risks and caveats associated with this have also considerably increased.
Among them, the most concerning and infuriating one is the failing of the Play Integrity Test [Basic, Device, and Strong]. While you can still pass this test via an unrevoked keybox XML file, however, it’s only a matter of time before this file gets revoked once again. And that’s the tip of the iceberg. The Widevine Certification failure leading to the inability to watch DRM-protected content like Netflix and Hulu only makes the matter worse.
Rounding it all off is the fact that you wouldn’t be able to use any banking and payment app of your choice either. Or is that really the case? Well, we found out a bunch of nifty hacks using which you can now address this problem once and for all. So without further ado, let’s check them out.
- How to Run Banking Apps on Rooted Android Devices [14 Methods] FIX 1: Via Magisk Alpha FIX 2: Via KernelSU/Next FIX 3: Pass Play Integrity Tests [Including Strong] FIX 4: Add App to Target File of Tricky Store FIX 5: Add to Magisk Denylist FIX 6: Enforce DenyList FIX 7: Hide Magisk App FIX 8: Use Zygisk Next FIX 9: Hide My Applist FIX 10: Delete Rooted APKs FIX 11: Use Root Detection Apps FIX 12: Using the Protect AI Bypass Module FIX 13: Switch to Unofficial Magisk FIX 14: Using KernelSU
How to Run Banking Apps on Rooted Android Devices [14 Methods]

There is no one fix that fits all. You’ll have to carry out each of the below-listed workarounds and then see which one works in your favor. In some cases, you might have to implement a combination of fixes for them to work effectively. All in all, it’s just a matter of permutations and combinations until you find the right fix for your banking app. So keeping these points in mind, let’s get started. Droidwin and its members wouldn’t be held responsible in case of a thermonuclear war, your alarm doesn’t wake you up, or if anything happens to your device and data by performing the below steps.

NOTE: In our comprehensive testing, we found out that FIX 1 and FIX 2 come with the highest success rate . So please try them first.
FIX 1: Via Magisk Alpha


You may download the Magisk Alpha app from any third-party site of your choice. As of now, we are using it from the Magisk Alpha Telegram group.
- First off, launch Magisk Alpha > go to Settings > Hide the Magisk app.
- Now go to Configure Denylist and enable the toggle next to these apps Google Play Services Google Play Store Google Services Framework Banking App Name
- Now create a blacklist using Hide My Applist and apply it to the desired bank app.
- Then pass at least the Device Integrity , though the Strong will be the best.
- Also, create a custom.pif.json file .
- Now, delete the data of Google Play Service, Google Play Store, Google Service Framework, and the bank app.
- Finally, restart your device and check out the result. If it’s still not working, then proceed with the below steps.
- Now go to the below location and open the target.txt file: data/adb/tricky_store/target.txt
- Then add its app package name in that text file and save it
- Again, delete the data of Google Play Service, Google Play Store, Google Service Framework, and the bank app.
- After that, spoof your device’s bootloader status to Locked . Finally, restart your device and check out the result.
FIX 2: Via KernelSU/Next
How to Run All Kotak Bank Apps on Rooted Android Device
- To begin with, it’s recommended to root your device using KernelSU / KernelSU Next app.
- Then launch it, go to Modules, and flash the SUSFS module [if supported by your kernel].
- Now create a blacklist using Hide My Applist and apply it to the bank app.
- Then pass at least the Device Integrity , though the Strong will be the best.
- Also, create a custom.pif.json file .
- Now go to the below location and open the target.txt file: data/adb/tricky_store/target.txt
- Then add its app package name in that text file and save it
- Now delete the data of Google Play Service, Google Play Store, Google Service Framework, and the banking app.
- Finally, restart your device and check out the result.
FIX 3: Pass Play Integrity Tests [Including Strong]
For most of you, this fix should be the only one that is required. Simply pass the Play Integrity Test [Basic, Device, and Strong] with the help of an unrevoked keybox XML file and you should be able to use banking and payment apps on your rooted devices without any issues. Confirmed working on apps like GPay [Google Pay] and PayTM. So refer to our below guide and get the job done right away:
How to Pass Play Integrity in New Android 13+ Checks
NOTE: Even if the above fix doesn’t work for you, then please do not remove any modules from your device as they will be needed in the subsequent fixes.
FIX 4: Add App to Target File of Tricky Store
Your next course of action should be to add the desired app to the target.txt file of the Tricky Store module. Here’s how it can be done:
- First off, find the app package name of your banking app.
- Then open File Manager and head to the below location: data/adb/trickystore
- Open the target.txt file and add the app’s package name.
- Hit the save icon > restart your device > check the result.
FIX 5: Add to Magisk Denylist
If the Tricky Store target file didn’t get the job done, then you should fall back to the earlier Magisk Hide feature and see if it does any good. Here’s how [as of now, do not delete the entry in the tricky store’s target.txt file]
- Launch Magisk > tap on the Settings icon > Configure Denylist.
- Enable the toggle next to your banking app and delete its data.
- Now restart your device and check whether it is working or not.
- If it is not working, then delete the entry from the target.txt file.
- Again restart the device, delete the app data, and see the result.
FIX 6: Enforce DenyList
Now consider forcibly enforcing the Denylist on your banking app by heading over to the Settings menu of Magisk and enabling the toggle next to Enforce Denylist. See if it spells out success for you or not. If it doesn’t then please disable this toggle right away because it tends to have an adverse impact on Shamiko and hence on the Tricky Store in general.


FIX 7: Hide Magisk App
Next up, consider hiding the Magisk app from its Settings menu and then see if the banking app is working on your rooted Android device or not.
![How to Run Banking Apps on Rooted Android Device [14 Methods] - 7](https://droidwin.com/wp-content/uploads/2025/02/hide-magisk-banking-app-rooted-android.jpg)
![How to Run Banking Apps on Rooted Android Device [14 Methods] - 8](https://droidwin.com/wp-content/uploads/2025/02/hide-magisk-banking-app-rooted-android.jpg)
FIX 8: Use Zygisk Next
Instead of the built-in Zygisk, you can also consider using the Zygisk Next module. Here’s how:
- Launch Magisk > go to its Settings> Disable Zygisk > restart the device.
- Download the Zygisk Next module > flash it via Magisk > restart device.
- Launch your Banking app and see if it is working along with root or not.
FIX 9: Hide My Applist
Next up, create a template having all the rooted apps within it [Magisk, LSPosed, root checker, modules, etc] and then hide that entire template from your banking app. Sounds difficult? Well, not at all because the Hide My Applist will take care of that with ease. Just refer to the below-linked guide and get the job done with ease.
How to Hide Root from Apps via Hide My Applist
FIX 10: Delete Rooted APKs
In some cases, banking apps might also scan your Internal storage for rooted APKs [see the next fix]. So if you have the likes of Magisk.apk, LSPosed.apk, twrp.img, etc, then please make sure to delete all those files and then try running your banking app.


FIX 11: Use Root Detection Apps
It might be the case that there are some rooted binaries left behind that you forget to hide or remove. Now, manually searching for all those files would end up taking ages. Therefore, you should instead consider using a root detection app to carry out this task. For instance, download and install the Ruru module from GitHub > enable with from LSPosed > launch it. Now have a look at all the Suspicious and/or Found entries in the list and address them accordingly.
How to Hide SU File and Magisk File
FIX 12: Using the Protect AI Bypass Module
How to Run iMobile on Rooted Android Device
FIX 13: Switch to Unofficial Magisk
If none of the aforementioned methods worked out for you, then you should consider switching over to an unofficial or the forked version of Magisk, such as Magisk Kitsune. Doing so might make it possible that the banking app could no longer detect the root app on your device. So refer to the below guide, make a switch right away, and check out the result.
How to Switch from Magisk to Kitsune
FIX 14: Using KernelSU
You can also consider completely ditching the Magisk ecosystem [official/unofficial] and instead switch over to KernelSU. To be more specific, uninstall Magisk and remove root, then root your device via KernelSU and pass the Play Integrity Test. After that, implement one of the fixes listed above and then check if you can achieve success or not. All of this guide has been explained in detail in the below guide, do have a look:
How to Hide Root via KernelSU on Rooted Android
- Starling Banking App not working in the rooted device [Fix]
- Banking/Payment Apps not working on non-rooted Samsung [Fix]
- Here’s why Pixel 7/Pro Face Unlock will not work with Banking Apps
- Mycanal/Canal+ Not Working on Rooted Android Device [Fixed]
- reforo 7 months ago Reply May I get the unrevoked xml file, please?
- abadi 9 months ago Reply Please give me the keybox.xml
- Aditya Vikram Singh 12 months ago Reply Please give me the keybox.xml file
- BRUNO 12 months ago Reply May I get the unrevoked xml file, please?
(Cancel Reply)
Δ
How to Get Fingerprint PIF.JSON File using Play Integrity Fork
In this guide, we will show you the steps to get the fingerprint PIF.JSON file using Play Integrity Fork. A week back or so, we got the unfortunate news that the Play Integrity Fix module has been discontinued by the developer chiteroman. We can’t thank him enough for the invaluable work he has done for this community. But going forward, what can be our next course of action?
Well, while this module was up and running, another developer [osm0sis] was also running a fork of this module, which goes by the name Play Integrity Fork. While we wouldn’t say that it was under the shadow of Fix, but it wasn’t being used that much when compared to its counterpart.

However, all that is about to change now, and so there are a few queries that might pop up in your minds. In this regard, one of the most common questions that I have been asked for the past week is how to get the fingerprint PIF.JSON file in the Play Integrity Fork module.
As you might already be aware, the Fix module already has this embedded in its module; you just need to launch it via KSUWebUI, hit the Fetch PIF.JSON option, and you’ll get the file. But that’s not possible via the Fork module via the direct route. Why? Let’s find out, and after that, we will list the plausible steps through which you can get this file using this module. Follow along.
- Why is the PIF JSON Fingerprint File Missing in Play Integrity Fork
- How to Get the Fingerprint PIF.JSON File using Play Integrity Fork
- Direct Download PIF JSON Files
Why is the PIF JSON Fingerprint File Missing in Play Integrity Fork
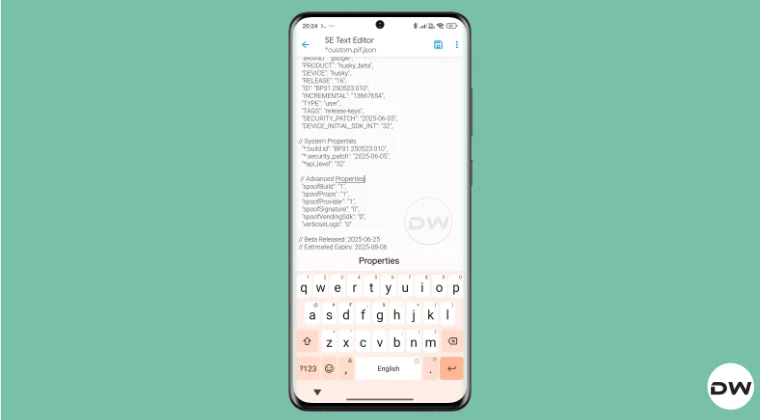
By default, the module comes with a template of a PIF JSON file that you need to fill in manually. You can get this file from /data/adb/modules/playintegrityfix. Once you fill in the values, simply rename it to custom.pif.json, and your task stands complete. But why hasn’t the dev simply added this file, as was the case with the Fix module? Here’s what he has to say regarding this:
There’s intentionally no pif.json in the module because the goal remains to be futureproof, and including something that may be banned and obsolete within days would be contrary to that goal.


However, finding these files might not be everyone’s cup of tea. Not only are a few of these remains, but finding them is also quite an effort taking task. The developer acknowledges this, and hence, he has added a script to extract the latest Pixel Beta fingerprint along with the module. The script is named autopif2, which generates a random device fingerprint from the latest Pixel Beta. So let’s have a look at the steps to make full use of this file.
How to Get the Fingerprint PIF.JSON File using Play Integrity Fork


Before starting, please take a backup of all the data on your device, just to be on the safe side. Droidwin and its members wouldn’t be held responsible in case of a thermonuclear war, your alarm doesn’t wake you up, or if anything happens to your device, and data by performing the below steps.
NOTE: There are quite a few ways of getting this job done, however, I personally found Termux to be the easiest among all of them. But if you want to try out any other method, then run the generation script from a root manager app that supports the module Action button or from a file explorer app that supports script execution.
- To begin with, flash the wget2 module via Magisk / KernelSU / APatch .
- Then, flash the Play Integrity Fork CI module from GitHub Actions .
- Now, download and install the Termux app from F-Droid.
- Then launch it and execute the following three commands: su //you’ll get a SU request, hit Grant cd /data/adb/modules/playintegrityfix //to change the directory to the module’s sh autopif2.sh –preview // this will give you the fingerprint file
- You can also add a few other parameters to the above command, namely: su -c sh /data/adb/modules/playintegrityfix/autopif2.sh -a -m -p -s -a Advanced -m Match -p Preview -s Strong
- Once done, head over to the below location to access the custom.pif.json /data/adb/modules/playintegrityfix
Direct Download PIF JSON Files
If you don’t want to manually carry out the aforementioned steps, then you may directly get the PIF JSON file from our below guide:
Download PIF JSON File from Here
- How to Pass Strong Integrity Using Revoked/Banned Keybox File!
- How to Pass Play Integrity in New Android 13+ Checks
- Guide to Pass Strong Integrity on Unlocked Bootloader & Root!
- How to Spoof/Fake/Hide Bootloader Unlock Status
- How to Pass Play Integrity Test on any Custom ROM [Video]
- Drw 6 months ago Reply Problem solved. Termux wasn’t prompting me to grant su user access. Found where to enable it in the KSU Next GUI under Superuser.
- Drw 6 months ago Reply I’m getting “su program not found.” Rooted with ksu and susfs. Modules installed are BKI, Play integrity fork, shamiko, susfs for ksu, tricky store, wget2, zygisk lsposed, and zygisk next. Nothing tweaked.
- mario 7 months ago Reply sorry, what do you mean with “Then, flash the Play Integrity Fork CI module from GitHub Actions.” ? i have pif v13 flashed in magisk
- Mohamed 7 months ago Reply Hi, can you please help me with a vaild keybox pleaaase 🙏
- Antonis 7 months ago Reply 1) “Then, flash the Play Integrity Fork CI module from GitHub Actions” https://github.com/osm0sis/PlayIntegrityFork/actions what do i download? 2) and then what do i do with custom.pif.json ?
- Antonis 7 months ago Reply “Then, flash the Play Integrity Fork CI module from GitHub Actions” https://github.com/osm0sis/PlayIntegrityFork/actions what do i download?
(Cancel Reply)
Δ
How to Run Banking Apps on Rooted Android Device [14 Methods]
In this guide, we will show you ten different methods using which you can run banking apps on your rooted Android device. Rooting is no longer what it used to be. Not only has the entire process undergone a major change thanks to the introduction of the init_boot partition, but the risks and caveats associated with this have also considerably increased.
Among them, the most concerning and infuriating one is the failing of the Play Integrity Test [Basic, Device, and Strong]. While you can still pass this test via an unrevoked keybox XML file, however, it’s only a matter of time before this file gets revoked once again. And that’s the tip of the iceberg. The Widevine Certification failure leading to the inability to watch DRM-protected content like Netflix and Hulu only makes the matter worse.
Rounding it all off is the fact that you wouldn’t be able to use any banking and payment app of your choice either. Or is that really the case? Well, we found out a bunch of nifty hacks using which you can now address this problem once and for all. So without further ado, let’s check them out.
- How to Run Banking Apps on Rooted Android Devices [14 Methods] FIX 1: Via Magisk Alpha FIX 2: Via KernelSU/Next FIX 3: Pass Play Integrity Tests [Including Strong] FIX 4: Add App to Target File of Tricky Store FIX 5: Add to Magisk Denylist FIX 6: Enforce DenyList FIX 7: Hide Magisk App FIX 8: Use Zygisk Next FIX 9: Hide My Applist FIX 10: Delete Rooted APKs FIX 11: Use Root Detection Apps FIX 12: Using the Protect AI Bypass Module FIX 13: Switch to Unofficial Magisk FIX 14: Using KernelSU
How to Run Banking Apps on Rooted Android Devices [14 Methods]

There is no one fix that fits all. You’ll have to carry out each of the below-listed workarounds and then see which one works in your favor. In some cases, you might have to implement a combination of fixes for them to work effectively. All in all, it’s just a matter of permutations and combinations until you find the right fix for your banking app. So keeping these points in mind, let’s get started. Droidwin and its members wouldn’t be held responsible in case of a thermonuclear war, your alarm doesn’t wake you up, or if anything happens to your device and data by performing the below steps.

NOTE: In our comprehensive testing, we found out that FIX 1 and FIX 2 come with the highest success rate . So please try them first.
FIX 1: Via Magisk Alpha


You may download the Magisk Alpha app from any third-party site of your choice. As of now, we are using it from the Magisk Alpha Telegram group.
- First off, launch Magisk Alpha > go to Settings > Hide the Magisk app.
- Now go to Configure Denylist and enable the toggle next to these apps Google Play Services Google Play Store Google Services Framework Banking App Name
- Now create a blacklist using Hide My Applist and apply it to the desired bank app.
- Then pass at least the Device Integrity , though the Strong will be the best.
- Also, create a custom.pif.json file .
- Now, delete the data of Google Play Service, Google Play Store, Google Service Framework, and the bank app.
- Finally, restart your device and check out the result. If it’s still not working, then proceed with the below steps.
- Now go to the below location and open the target.txt file: data/adb/tricky_store/target.txt
- Then add its app package name in that text file and save it
- Again, delete the data of Google Play Service, Google Play Store, Google Service Framework, and the bank app.
- After that, spoof your device’s bootloader status to Locked . Finally, restart your device and check out the result.
FIX 2: Via KernelSU/Next
How to Run All Kotak Bank Apps on Rooted Android Device
- To begin with, it’s recommended to root your device using KernelSU / KernelSU Next app.
- Then launch it, go to Modules, and flash the SUSFS module [if supported by your kernel].
- Now create a blacklist using Hide My Applist and apply it to the bank app.
- Then pass at least the Device Integrity , though the Strong will be the best.
- Also, create a custom.pif.json file .
- Now go to the below location and open the target.txt file: data/adb/tricky_store/target.txt
- Then add its app package name in that text file and save it
- Now delete the data of Google Play Service, Google Play Store, Google Service Framework, and the banking app.
- Finally, restart your device and check out the result.
FIX 3: Pass Play Integrity Tests [Including Strong]
For most of you, this fix should be the only one that is required. Simply pass the Play Integrity Test [Basic, Device, and Strong] with the help of an unrevoked keybox XML file and you should be able to use banking and payment apps on your rooted devices without any issues. Confirmed working on apps like GPay [Google Pay] and PayTM. So refer to our below guide and get the job done right away:
How to Pass Play Integrity in New Android 13+ Checks
NOTE: Even if the above fix doesn’t work for you, then please do not remove any modules from your device as they will be needed in the subsequent fixes.
FIX 4: Add App to Target File of Tricky Store
Your next course of action should be to add the desired app to the target.txt file of the Tricky Store module. Here’s how it can be done:
- First off, find the app package name of your banking app.
- Then open File Manager and head to the below location: data/adb/trickystore
- Open the target.txt file and add the app’s package name.
- Hit the save icon > restart your device > check the result.
FIX 5: Add to Magisk Denylist
If the Tricky Store target file didn’t get the job done, then you should fall back to the earlier Magisk Hide feature and see if it does any good. Here’s how [as of now, do not delete the entry in the tricky store’s target.txt file]
- Launch Magisk > tap on the Settings icon > Configure Denylist.
- Enable the toggle next to your banking app and delete its data.
- Now restart your device and check whether it is working or not.
- If it is not working, then delete the entry from the target.txt file.
- Again restart the device, delete the app data, and see the result.
FIX 6: Enforce DenyList
Now consider forcibly enforcing the Denylist on your banking app by heading over to the Settings menu of Magisk and enabling the toggle next to Enforce Denylist. See if it spells out success for you or not. If it doesn’t then please disable this toggle right away because it tends to have an adverse impact on Shamiko and hence on the Tricky Store in general.


FIX 7: Hide Magisk App
Next up, consider hiding the Magisk app from its Settings menu and then see if the banking app is working on your rooted Android device or not.
![How to Run Banking Apps on Rooted Android Device [14 Methods] - 27](https://droidwin.com/wp-content/uploads/2025/02/hide-magisk-banking-app-rooted-android.jpg)
![How to Run Banking Apps on Rooted Android Device [14 Methods] - 28](https://droidwin.com/wp-content/uploads/2025/02/hide-magisk-banking-app-rooted-android.jpg)
FIX 8: Use Zygisk Next
Instead of the built-in Zygisk, you can also consider using the Zygisk Next module. Here’s how:
- Launch Magisk > go to its Settings> Disable Zygisk > restart the device.
- Download the Zygisk Next module > flash it via Magisk > restart device.
- Launch your Banking app and see if it is working along with root or not.
FIX 9: Hide My Applist
Next up, create a template having all the rooted apps within it [Magisk, LSPosed, root checker, modules, etc] and then hide that entire template from your banking app. Sounds difficult? Well, not at all because the Hide My Applist will take care of that with ease. Just refer to the below-linked guide and get the job done with ease.
How to Hide Root from Apps via Hide My Applist
FIX 10: Delete Rooted APKs
In some cases, banking apps might also scan your Internal storage for rooted APKs [see the next fix]. So if you have the likes of Magisk.apk, LSPosed.apk, twrp.img, etc, then please make sure to delete all those files and then try running your banking app.


FIX 11: Use Root Detection Apps
It might be the case that there are some rooted binaries left behind that you forget to hide or remove. Now, manually searching for all those files would end up taking ages. Therefore, you should instead consider using a root detection app to carry out this task. For instance, download and install the Ruru module from GitHub > enable with from LSPosed > launch it. Now have a look at all the Suspicious and/or Found entries in the list and address them accordingly.
How to Hide SU File and Magisk File
FIX 12: Using the Protect AI Bypass Module
How to Run iMobile on Rooted Android Device
FIX 13: Switch to Unofficial Magisk
If none of the aforementioned methods worked out for you, then you should consider switching over to an unofficial or the forked version of Magisk, such as Magisk Kitsune. Doing so might make it possible that the banking app could no longer detect the root app on your device. So refer to the below guide, make a switch right away, and check out the result.
How to Switch from Magisk to Kitsune
FIX 14: Using KernelSU
You can also consider completely ditching the Magisk ecosystem [official/unofficial] and instead switch over to KernelSU. To be more specific, uninstall Magisk and remove root, then root your device via KernelSU and pass the Play Integrity Test. After that, implement one of the fixes listed above and then check if you can achieve success or not. All of this guide has been explained in detail in the below guide, do have a look:
How to Hide Root via KernelSU on Rooted Android
- Starling Banking App not working in the rooted device [Fix]
- Banking/Payment Apps not working on non-rooted Samsung [Fix]
- Here’s why Pixel 7/Pro Face Unlock will not work with Banking Apps
- Mycanal/Canal+ Not Working on Rooted Android Device [Fixed]
- reforo 7 months ago Reply May I get the unrevoked xml file, please?
- abadi 9 months ago Reply Please give me the keybox.xml
- Aditya Vikram Singh 12 months ago Reply Please give me the keybox.xml file
- BRUNO 12 months ago Reply May I get the unrevoked xml file, please?
(Cancel Reply)
Δ
How to Run Banking Apps on Rooted Android Device [14 Methods]
In this guide, we will show you ten different methods using which you can run banking apps on your rooted Android device. Rooting is no longer what it used to be. Not only has the entire process undergone a major change thanks to the introduction of the init_boot partition, but the risks and caveats associated with this have also considerably increased.
Among them, the most concerning and infuriating one is the failing of the Play Integrity Test [Basic, Device, and Strong]. While you can still pass this test via an unrevoked keybox XML file, however, it’s only a matter of time before this file gets revoked once again. And that’s the tip of the iceberg. The Widevine Certification failure leading to the inability to watch DRM-protected content like Netflix and Hulu only makes the matter worse.
Rounding it all off is the fact that you wouldn’t be able to use any banking and payment app of your choice either. Or is that really the case? Well, we found out a bunch of nifty hacks using which you can now address this problem once and for all. So without further ado, let’s check them out.
- How to Run Banking Apps on Rooted Android Devices [14 Methods] FIX 1: Via Magisk Alpha FIX 2: Via KernelSU/Next FIX 3: Pass Play Integrity Tests [Including Strong] FIX 4: Add App to Target File of Tricky Store FIX 5: Add to Magisk Denylist FIX 6: Enforce DenyList FIX 7: Hide Magisk App FIX 8: Use Zygisk Next FIX 9: Hide My Applist FIX 10: Delete Rooted APKs FIX 11: Use Root Detection Apps FIX 12: Using the Protect AI Bypass Module FIX 13: Switch to Unofficial Magisk FIX 14: Using KernelSU
How to Run Banking Apps on Rooted Android Devices [14 Methods]

There is no one fix that fits all. You’ll have to carry out each of the below-listed workarounds and then see which one works in your favor. In some cases, you might have to implement a combination of fixes for them to work effectively. All in all, it’s just a matter of permutations and combinations until you find the right fix for your banking app. So keeping these points in mind, let’s get started. Droidwin and its members wouldn’t be held responsible in case of a thermonuclear war, your alarm doesn’t wake you up, or if anything happens to your device and data by performing the below steps.

NOTE: In our comprehensive testing, we found out that FIX 1 and FIX 2 come with the highest success rate . So please try them first.
FIX 1: Via Magisk Alpha


You may download the Magisk Alpha app from any third-party site of your choice. As of now, we are using it from the Magisk Alpha Telegram group.
- First off, launch Magisk Alpha > go to Settings > Hide the Magisk app.
- Now go to Configure Denylist and enable the toggle next to these apps Google Play Services Google Play Store Google Services Framework Banking App Name
- Now create a blacklist using Hide My Applist and apply it to the desired bank app.
- Then pass at least the Device Integrity , though the Strong will be the best.
- Also, create a custom.pif.json file .
- Now, delete the data of Google Play Service, Google Play Store, Google Service Framework, and the bank app.
- Finally, restart your device and check out the result. If it’s still not working, then proceed with the below steps.
- Now go to the below location and open the target.txt file: data/adb/tricky_store/target.txt
- Then add its app package name in that text file and save it
- Again, delete the data of Google Play Service, Google Play Store, Google Service Framework, and the bank app.
- After that, spoof your device’s bootloader status to Locked . Finally, restart your device and check out the result.
FIX 2: Via KernelSU/Next
How to Run All Kotak Bank Apps on Rooted Android Device
- To begin with, it’s recommended to root your device using KernelSU / KernelSU Next app.
- Then launch it, go to Modules, and flash the SUSFS module [if supported by your kernel].
- Now create a blacklist using Hide My Applist and apply it to the bank app.
- Then pass at least the Device Integrity , though the Strong will be the best.
- Also, create a custom.pif.json file .
- Now go to the below location and open the target.txt file: data/adb/tricky_store/target.txt
- Then add its app package name in that text file and save it
- Now delete the data of Google Play Service, Google Play Store, Google Service Framework, and the banking app.
- Finally, restart your device and check out the result.
FIX 3: Pass Play Integrity Tests [Including Strong]
For most of you, this fix should be the only one that is required. Simply pass the Play Integrity Test [Basic, Device, and Strong] with the help of an unrevoked keybox XML file and you should be able to use banking and payment apps on your rooted devices without any issues. Confirmed working on apps like GPay [Google Pay] and PayTM. So refer to our below guide and get the job done right away:
How to Pass Play Integrity in New Android 13+ Checks
NOTE: Even if the above fix doesn’t work for you, then please do not remove any modules from your device as they will be needed in the subsequent fixes.
FIX 4: Add App to Target File of Tricky Store
Your next course of action should be to add the desired app to the target.txt file of the Tricky Store module. Here’s how it can be done:
- First off, find the app package name of your banking app.
- Then open File Manager and head to the below location: data/adb/trickystore
- Open the target.txt file and add the app’s package name.
- Hit the save icon > restart your device > check the result.
FIX 5: Add to Magisk Denylist
If the Tricky Store target file didn’t get the job done, then you should fall back to the earlier Magisk Hide feature and see if it does any good. Here’s how [as of now, do not delete the entry in the tricky store’s target.txt file]
- Launch Magisk > tap on the Settings icon > Configure Denylist.
- Enable the toggle next to your banking app and delete its data.
- Now restart your device and check whether it is working or not.
- If it is not working, then delete the entry from the target.txt file.
- Again restart the device, delete the app data, and see the result.
FIX 6: Enforce DenyList
Now consider forcibly enforcing the Denylist on your banking app by heading over to the Settings menu of Magisk and enabling the toggle next to Enforce Denylist. See if it spells out success for you or not. If it doesn’t then please disable this toggle right away because it tends to have an adverse impact on Shamiko and hence on the Tricky Store in general.


FIX 7: Hide Magisk App
Next up, consider hiding the Magisk app from its Settings menu and then see if the banking app is working on your rooted Android device or not.
![How to Run Banking Apps on Rooted Android Device [14 Methods] - 39](https://droidwin.com/wp-content/uploads/2025/02/hide-magisk-banking-app-rooted-android.jpg)
![How to Run Banking Apps on Rooted Android Device [14 Methods] - 40](https://droidwin.com/wp-content/uploads/2025/02/hide-magisk-banking-app-rooted-android.jpg)
FIX 8: Use Zygisk Next
Instead of the built-in Zygisk, you can also consider using the Zygisk Next module. Here’s how:
- Launch Magisk > go to its Settings> Disable Zygisk > restart the device.
- Download the Zygisk Next module > flash it via Magisk > restart device.
- Launch your Banking app and see if it is working along with root or not.
FIX 9: Hide My Applist
Next up, create a template having all the rooted apps within it [Magisk, LSPosed, root checker, modules, etc] and then hide that entire template from your banking app. Sounds difficult? Well, not at all because the Hide My Applist will take care of that with ease. Just refer to the below-linked guide and get the job done with ease.
How to Hide Root from Apps via Hide My Applist
FIX 10: Delete Rooted APKs
In some cases, banking apps might also scan your Internal storage for rooted APKs [see the next fix]. So if you have the likes of Magisk.apk, LSPosed.apk, twrp.img, etc, then please make sure to delete all those files and then try running your banking app.


FIX 11: Use Root Detection Apps
It might be the case that there are some rooted binaries left behind that you forget to hide or remove. Now, manually searching for all those files would end up taking ages. Therefore, you should instead consider using a root detection app to carry out this task. For instance, download and install the Ruru module from GitHub > enable with from LSPosed > launch it. Now have a look at all the Suspicious and/or Found entries in the list and address them accordingly.
How to Hide SU File and Magisk File
FIX 12: Using the Protect AI Bypass Module
How to Run iMobile on Rooted Android Device
FIX 13: Switch to Unofficial Magisk
If none of the aforementioned methods worked out for you, then you should consider switching over to an unofficial or the forked version of Magisk, such as Magisk Kitsune. Doing so might make it possible that the banking app could no longer detect the root app on your device. So refer to the below guide, make a switch right away, and check out the result.
How to Switch from Magisk to Kitsune
FIX 14: Using KernelSU
You can also consider completely ditching the Magisk ecosystem [official/unofficial] and instead switch over to KernelSU. To be more specific, uninstall Magisk and remove root, then root your device via KernelSU and pass the Play Integrity Test. After that, implement one of the fixes listed above and then check if you can achieve success or not. All of this guide has been explained in detail in the below guide, do have a look:
How to Hide Root via KernelSU on Rooted Android
- Starling Banking App not working in the rooted device [Fix]
- Banking/Payment Apps not working on non-rooted Samsung [Fix]
- Here’s why Pixel 7/Pro Face Unlock will not work with Banking Apps
- Mycanal/Canal+ Not Working on Rooted Android Device [Fixed]
- reforo 7 months ago Reply May I get the unrevoked xml file, please?
- abadi 9 months ago Reply Please give me the keybox.xml
- Aditya Vikram Singh 12 months ago Reply Please give me the keybox.xml file
- BRUNO 12 months ago Reply May I get the unrevoked xml file, please?
(Cancel Reply)
Δ
How to Root any OnePlus via KernelSU Next and SUSFS
In this guide, we will show you the steps to root your OnePlus device using KernelSU Next and SUSFS. When it comes to gaining administrative privileges over your device, Magisk has long been the go-to choice for tech enthusiasts. However, over the last few months, we have witnessed a slight change in this trend, with many people moving towards KernelSU.
One major reason for the same is the issues with hiding the root when it comes to Magisk. Even if you end up passing the Basic and Device test [well, in some cases, even the Strong Test] and hide the Magisk app, the banking and payment apps will still end up identifying that your device is rooted via Magisk, and hence they will refuse to function.
Fortunately, at least for now, that isn’t the case with KernelSU. This, when combined with the SUSFS, gives you the most stringent root hiding environment along with a slew of additional advanced-level tweaks. So, without any further ado, let’s make you aware of the steps to root your OnePlus device using the combination of KernelSU Next and SUSFS. Follow along.
- How to Root any OnePlus Phone via KernelSU Next and SUSFS SUPPORTED DEVICE LIST INSTALLATION STEPS
- How to Install OnePlus Kernel with KernelSU Next without TWRP
How to Root any OnePlus Phone via KernelSU Next and SUSFS

Before starting, take a backup of all the data on your device, just to be on the safe side. Droidwin and its members wouldn’t be held responsible in case of a thermonuclear war, your alarm doesn’t wake you up, or if anything happens to your device, and data by performing the below steps.
SUPPORTED DEVICE LIST
As of now, these are the supported devices, though more devices will be added in the near future, so stay tuned!
OP ACE 2 PRO
OP ACE 2
OP ACE 3V
OP ACE 5
OP ACE 5 PRO
OP NORD 4
OP OPEN
OP PAD 2
OP 10 PRO
OP 10T
OP 11R
OP 11
OP 12
OP 12R
OP 13
OP 13R
OP 13S
INSTALLATION STEPS

- First off, download the required files from below: OnePlus Kernel with KernelSU Next and SUSFS Support KernelSU Next App SUSFS Module
- Then install the TWRP Recovery onto your device.
- Now reboot your device to TWRP Recovery using: adb reboot recovery // from the OS fastboot reboot recovery // from Fastboot Mode
- Now go to Install > select the OnePlus Kernel > flash it.
- Then go to Reboot and select System to boot to the OS.
- Next up, install the KernelSU Next app. Then launch it.
- Go to Modules, tap Install, and flash the SUSFS Module.
- Now, hit Reboot. Once it boots up, tap Open next to SUSFS.
- Then tap on Custom SUSFS Settings and customize it as per your liking.
- How to Root OnePlus 13 via KernelSU Next and SUSFS
- How to Root OnePlus 11 using KernelSU Next and SUSFS
- Detailed Guide to Hide Root via KernelSU on Rooted Android
- How to Install OTA Updates on Rooted Device via KernelSU
How to Install OnePlus Kernel with KernelSU Next without TWRP


Some OnePlus devices might not have a working TWRP Recovery. So in such cases, here’s what you need to do:
- First off, download the required files from below: OnePlus Kernel with KernelSU Next and SUSFS Support KernelSU Next App SUSFS Module
- Download the same firmware which is installed on your device.
- Then extract the init_boot.img from it using Fastboot Enhance.
- Now transfer the file to your device. Then install KernelSU Next.
- Launch it, tap on the downward arrow > select a file > init_boot.
- File will now be patched. Transfer it to the platform-tools folder.
- Now open the Command Prompt inside the platform-tools folder.
- Then type in the below command to boot your device to Fastboot. adb reboot bootloader
- Now type in the below command to flash this patched init_boot: fastboot flash init_boot patched_init_boot.img
- Then type the below command to boot the device to the rooted OS fastboot reboot
- Install the Kernel Flasher app , launch it, and tap View next to both slots.
- Then note down the Slot name [A or B] that gives you the Flash option.
- Now tap on Flash > Flash AK3 ZIP > select the OnePlus Kernel.
- Once done, restart the device for the kernel to be up and running.
- Next up, install the KernelSU Next app. Then launch it.
- Go to Modules, tap Install, and flash the SUSFS Module.
- Now, hit Reboot. Once it boots up, tap Open next to SUSFS.
- Then tap on Custom SUSFS Settings and customize it as per your liking.
- ae 3 months ago Reply does it not work on oxygenos 16 because the apps are no longer being granted root access
- Akash 5 months ago Reply Need kernal su file for oneplus 8 pro running 13
(Cancel Reply)
Δ