Keybox Might No Longer Work from February 2026!
Any and every rooted user knows the drill by now- flash a bunch of modules like Tricky Store and PIF, get an unrevoked keybox file , and place it in data > adb > tricky_store directory. That’s it. You will now pass Strong Integrity and will be able to use banking apps with ease [in some cases, apps like HideMApplist might be required too]. However, all of this might be a thing of the past. Beginning with February 2026, these keybox files will be of no use, all thanks to Google. But why is that the case?
Why Will Keybox Not Work from February 2026?

This is because Remote Key Provisioning keys will become mandatory for devices supporting RKP (i.e., phones released with Android 13+). As a result of this, phones with an unlocked bootloader would no longer be able to pass Device or Strong Integrity . RKP provisioning servers will issue keys signed with the new RSA-4096 attestation signing root certificate from February. According to Google:
• Devices that use Remote Key Provisioning (RKP) will begin receiving certificates rooted in this new certificate in February 2026. • RKP-enabled devices will exclusively use the new root by April 10, 2026.
So, using TrickyStore (or similar) to get DEVICE or BASIC integrity using leaked OEM keys will no longer be possible on these devices , as they will effectively be blocked from using the old RSA-2048 root. The changes will impact both the devices with broken and unbroken TEE.
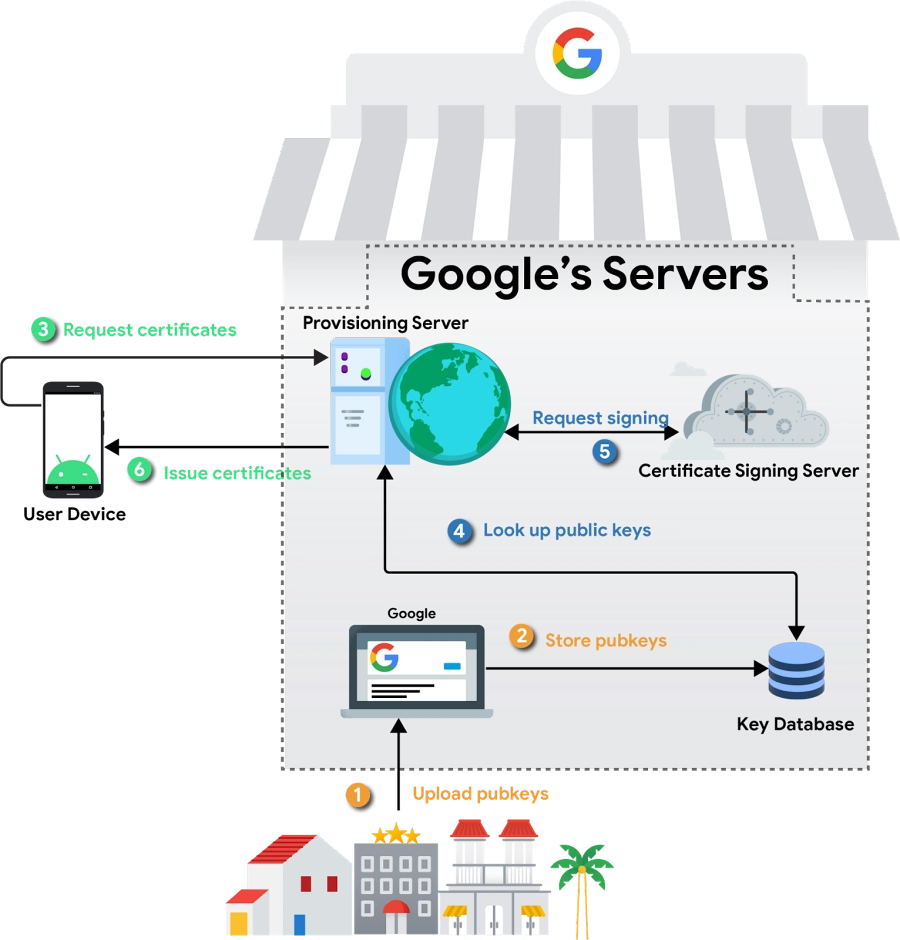
Credits: Google
The switch will be made at the beginning of February, but with the life span of RKP certs set to about 2 months at the moment (they’ll be reduced to 45 days over the next year or so), it will take till April 10 before all affected devices have keys signed by the new 2026 root and block the old one (RSA-2048).
In short, starting February 2026, RKP devices will start using certificates signed with the new attestation root. By April ,10 2026, all RKP-enabled devices must only use the new root certificates. As a result of this, Keybox workarounds that depend on the old attestation root certificate will no longer work.
Any Excluded Devices
The Pixel 6 series might be excluded from this new RKM fiasco. But why? They will most likely be whitelisted due to the anomaly with the Titan M2 not having native RKP (only TEE does) due to early StrongBox firmware, and hence they will still use the old attestation root (RSA-2048).
This is a developing story and will be updated at regular intervals. So stay tuned. We would like to thank XDA Senior Developers zgfg and pndwal for this information. Moreover, you may read the official announcement by Google here .
- How to Get Fingerprint PIF.JSON File using Play Integrity Fork
- Droidwin Keybox Module: Gives You a New Unrevoked Keybox!
- Get an Unrevoked Keybox XML File Here | Pass Strong Integrity
- Download PIF JSON File from Here
- Tricky Store now has its open source alternative!
(Cancel Reply)
Δ
How to Get Fingerprint PIF.JSON File using Play Integrity Fork
In this guide, we will show you the steps to get the fingerprint PIF.JSON file using Play Integrity Fork. A week back or so, we got the unfortunate news that the Play Integrity Fix module has been discontinued by the developer chiteroman. We can’t thank him enough for the invaluable work he has done for this community. But going forward, what can be our next course of action?
Well, while this module was up and running, another developer [osm0sis] was also running a fork of this module, which goes by the name Play Integrity Fork. While we wouldn’t say that it was under the shadow of Fix, but it wasn’t being used that much when compared to its counterpart.

However, all that is about to change now, and so there are a few queries that might pop up in your minds. In this regard, one of the most common questions that I have been asked for the past week is how to get the fingerprint PIF.JSON file in the Play Integrity Fork module.
As you might already be aware, the Fix module already has this embedded in its module; you just need to launch it via KSUWebUI, hit the Fetch PIF.JSON option, and you’ll get the file. But that’s not possible via the Fork module via the direct route. Why? Let’s find out, and after that, we will list the plausible steps through which you can get this file using this module. Follow along.
- Why is the PIF JSON Fingerprint File Missing in Play Integrity Fork
- How to Get the Fingerprint PIF.JSON File using Play Integrity Fork
- Direct Download PIF JSON Files
Why is the PIF JSON Fingerprint File Missing in Play Integrity Fork
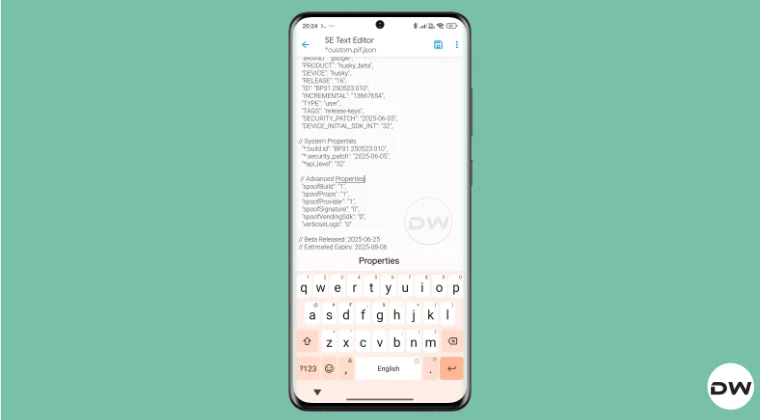
By default, the module comes with a template of a PIF JSON file that you need to fill in manually. You can get this file from /data/adb/modules/playintegrityfix. Once you fill in the values, simply rename it to custom.pif.json, and your task stands complete. But why hasn’t the dev simply added this file, as was the case with the Fix module? Here’s what he has to say regarding this:
There’s intentionally no pif.json in the module because the goal remains to be futureproof, and including something that may be banned and obsolete within days would be contrary to that goal.


However, finding these files might not be everyone’s cup of tea. Not only are a few of these remains, but finding them is also quite an effort taking task. The developer acknowledges this, and hence, he has added a script to extract the latest Pixel Beta fingerprint along with the module. The script is named autopif2, which generates a random device fingerprint from the latest Pixel Beta. So let’s have a look at the steps to make full use of this file.
How to Get the Fingerprint PIF.JSON File using Play Integrity Fork


Before starting, please take a backup of all the data on your device, just to be on the safe side. Droidwin and its members wouldn’t be held responsible in case of a thermonuclear war, your alarm doesn’t wake you up, or if anything happens to your device, and data by performing the below steps.
NOTE: There are quite a few ways of getting this job done, however, I personally found Termux to be the easiest among all of them. But if you want to try out any other method, then run the generation script from a root manager app that supports the module Action button or from a file explorer app that supports script execution.
- To begin with, flash the wget2 module via Magisk / KernelSU / APatch .
- Then, flash the Play Integrity Fork CI module from GitHub Actions .
- Now, download and install the Termux app from F-Droid.
- Then launch it and execute the following three commands: su //you’ll get a SU request, hit Grant cd /data/adb/modules/playintegrityfix //to change the directory to the module’s sh autopif2.sh –preview // this will give you the fingerprint file
- You can also add a few other parameters to the above command, namely: su -c sh /data/adb/modules/playintegrityfix/autopif2.sh -a -m -p -s -a Advanced -m Match -p Preview -s Strong
- Once done, head over to the below location to access the custom.pif.json /data/adb/modules/playintegrityfix
Direct Download PIF JSON Files
If you don’t want to manually carry out the aforementioned steps, then you may directly get the PIF JSON file from our below guide:
Download PIF JSON File from Here
- How to Pass Strong Integrity Using Revoked/Banned Keybox File!
- How to Pass Play Integrity in New Android 13+ Checks
- Guide to Pass Strong Integrity on Unlocked Bootloader & Root!
- How to Spoof/Fake/Hide Bootloader Unlock Status
- How to Pass Play Integrity Test on any Custom ROM [Video]
- Drw 6 months ago Reply Problem solved. Termux wasn’t prompting me to grant su user access. Found where to enable it in the KSU Next GUI under Superuser.
- Drw 6 months ago Reply I’m getting “su program not found.” Rooted with ksu and susfs. Modules installed are BKI, Play integrity fork, shamiko, susfs for ksu, tricky store, wget2, zygisk lsposed, and zygisk next. Nothing tweaked.
- mario 7 months ago Reply sorry, what do you mean with “Then, flash the Play Integrity Fork CI module from GitHub Actions.” ? i have pif v13 flashed in magisk
- Mohamed 7 months ago Reply Hi, can you please help me with a vaild keybox pleaaase 🙏
- Antonis 7 months ago Reply 1) “Then, flash the Play Integrity Fork CI module from GitHub Actions” https://github.com/osm0sis/PlayIntegrityFork/actions what do i download? 2) and then what do i do with custom.pif.json ?
- Antonis 7 months ago Reply “Then, flash the Play Integrity Fork CI module from GitHub Actions” https://github.com/osm0sis/PlayIntegrityFork/actions what do i download?
(Cancel Reply)
Δ